We Stop Threats.
At Machine
Speed.
Active breaches contained in under 3 minutes. Automatically. No alert queues. No analyst backlog. 680,000 assets protected worldwide.
On-Demand Webinar
Why Cloud Security Tools Are Missing the Attacks That Matter
Attackers move through legitimate APIs. See how PulseADT closes the gap your current stack leaves open.
Learn morePlatform
Respond in Minutes. Automatically.
PulseADT contains active threats autonomously - within the boundaries you define. Your team sees outcomes, not queues.
Learn moreOn-Demand Webinar
Pass Your Next Audit Without the Scramble
Every PulseADT response generates a complete evidence trail. Regulators get what they need. Your team keeps moving.
Learn moreThreat Detection & Response
Stop breaches before they spread.
PulseADT detects active intrusions across your cloud, identity, and infrastructure layers - then contains them automatically in under 3 minutes. Your analysts see outcomes, not alert queues.
- 95% of threats auto-contained without human intervention
- 359× faster detection than industry average
- Zero-touch isolation - sessions, tokens, and privileges revoked instantly
Adversary Intelligence
Know who's targeting you. Before they move.
Glemad tracks 200+ active threat actors - APTs, ransomware groups, and nation-state operators. Every detection is mapped to a known adversary profile, so your team understands the threat, not just the alert.
- 200+ adversary profiles updated in real time
- MITRE ATT&CK mapped - every TTP, every campaign
- Intersect live threat intel against your specific environment
AI Reasoning Engine
Every action traceable. Every decision defensible.
PulseADT doesn't just act - it reasons. Every automated response is logged with a full evidence chain: what was observed, why action was taken, and what constraints were checked. Walk into any audit with confidence.
- 100% MITRE ATT&CK coverage - no blind spots
- Audit-ready evidence bundle generated on every incident
- 97% intent classification accuracy across all decisions
Glemad Research · PulseADT Independent Threat Intelligence Lab
March 2026 Milestone Report
Independent benchmarks across 680,000 protected assets. Throughput, containment speed, and growth - verified by Glemad Research.
Sustained event processing throughput
99.7% uptime across all tenants
Concurrent multi-step threat hypotheses
Tracked simultaneously in real time
Growth in assets protected
January 2025 → March 2026
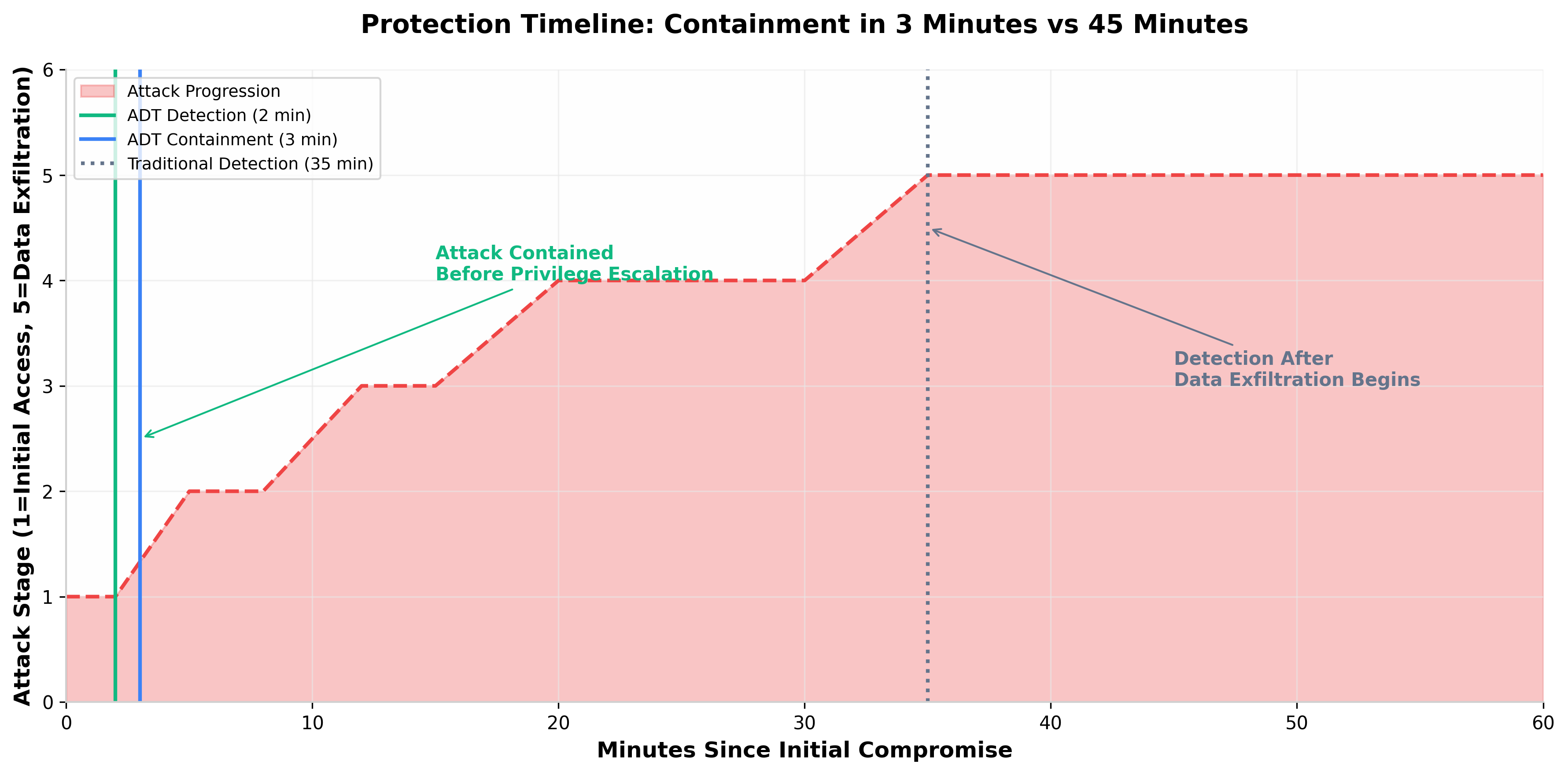
Protection timeline
Contained in 3 minutes.
Traditional tools detect at minute 35.
In a real cloud identity compromise scenario, PulseADT detects the anomalous authentication, revokes the compromised session, and suspends escalated privileges within 3 minutes. Traditional detection triggers at minute 35 - after lateral movement and data exfiltration have already begun.
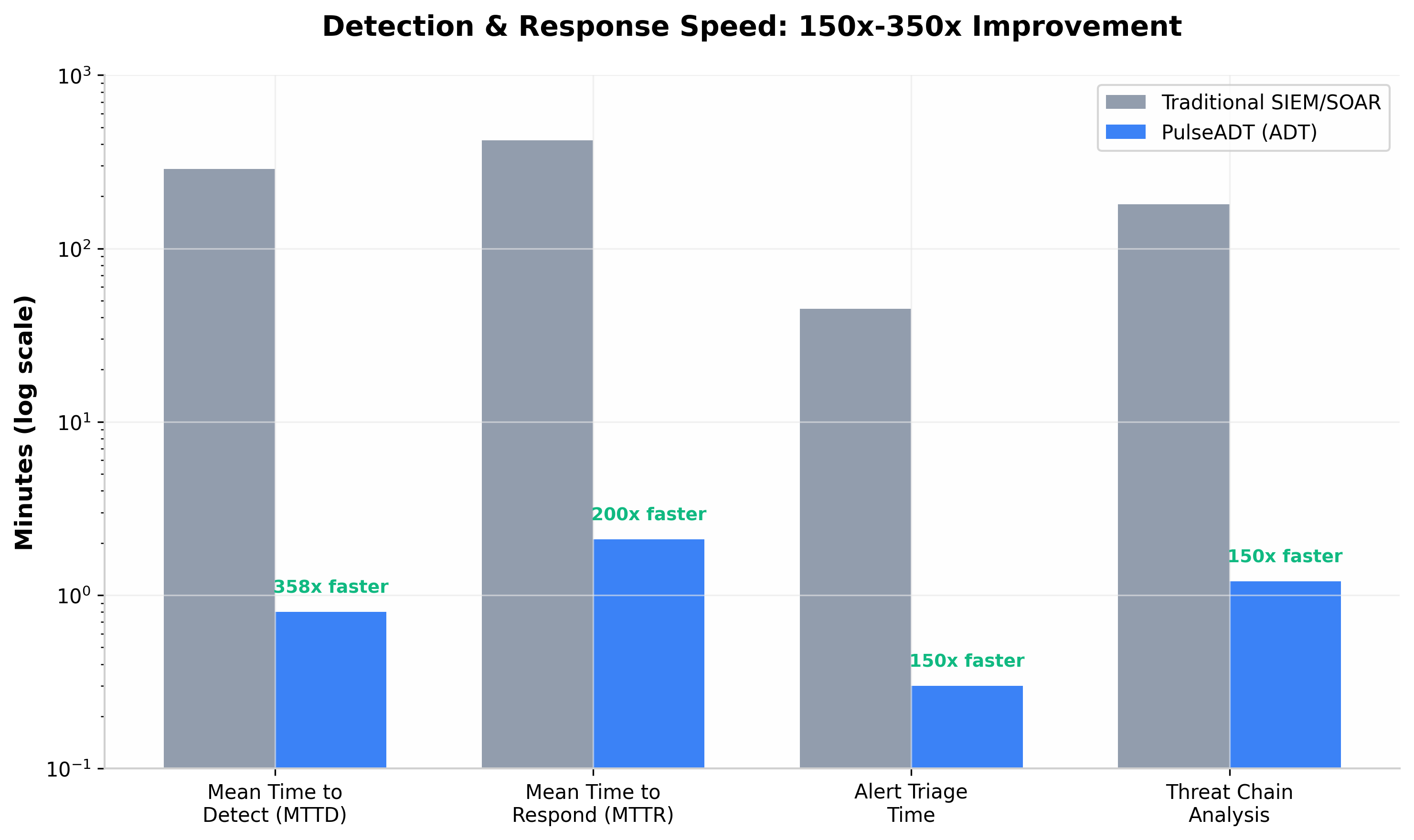
Detection speed
Not incrementally faster.
Categorically different.
The 359× improvement in detection speed is not an optimization. It is the difference between human-paced and machine-paced defense - a closed-loop AI that reasons continuously, not a triage queue waiting for an analyst.
vs. 287 min industry average
Why PulseADT
Detect faster. Contain automatically.
Pass every audit.
PulseADT protects your infrastructure around the clock - detecting threats, responding autonomously, and generating the evidence your compliance teams need.
Respond Before Damage Is Done
PulseADT detects active intrusions and contains them autonomously - shrinking your risk window from hours to seconds. No alert queues, no analyst backlog.
Stop Attacks Your Other Tools Miss
Cloud, identity, CI/CD, and network - PulseADT correlates signals across every domain. Multi-step attacks that siloed tools miss entirely are caught before privilege escalation completes.
Compliance Evidence, Automatically
Every response action is documented with full justification and audit trail. Reduce compliance preparation from weeks to hours. Walk into any regulatory review with confidence.
Industry Recognition
Recognised by analysts.
Validated by results.
Glemad has been named a Leader in three consecutive analyst evaluations across cloud security, MDR, and identity threat detection - independently validated against real-world attack scenarios.
Gartner® Magic Quadrant™
Leader - Cloud-Native App Protection (CNAPP)
Third consecutive year. Evaluated on endpoint, cloud, and identity coverage.
Download reportGartner® Peer Insights™
Customers’ Choice 2025
Voice of the Customer for Cloud Security Posture Management - recognised by verified users.
Read reviewsIDC MarketScape
Leader - Worldwide MDR Services 2025
Cited for autonomous actuation capability and audit-grade evidence generation.
Download excerptPricing
Simple, transparent pricing.
Every tier detects the same threats. What changes is how far PulseADT acts on them.
Eagle Reason
Continuous visibility across cloud, identity, and endpoint - with analyst-ready, hypothesis-chain alerts.
Min. 500 assets
- Cloud, identity & endpoint monitoring
- Hypothesis-chain alert reasoning
- MITRE ATT&CK correlation
- Compliance audit logs (SOC 2 / ISO 27001)
- Glemad threat intelligence feed
- 90-day data retention
- API access
- Email & chat support
- Autonomous containment
- Automated remediation
Eagle Pro
Autonomous containment - isolate threats, revoke credentials, and block lateral movement without analyst intervention.
Min. 500 assets
- Everything in Eagle Reason
- Autonomous Class 1 response (policy-bounded)
- Contain: isolate, block, revoke credentials
- Real-time actuation audit trail
- Custom response policies
- 1-year data retention
- Priority support (4-hr SLA)
- SIEM / SOAR integration
- Automated remediation (Class 2)
Eagle Max
Full-spectrum autonomous defense. Detect, contain, remediate, and recover - with verifiable evidence for every action.
Volume discounts available
- Everything in Eagle Pro
- Autonomous Class 2 response (remediate & recover)
- Policy negotiation & custom actuation rules
- Dedicated customer success manager
- Custom integrations & on-premise deployment
- Unlimited data retention
- 24/7 phone + Slack support
- SLA guarantees (99.9% uptime)
Golden Eagle Enterprise
Custom deployment, dedicated engineering, and managed response for organisations operating at scale.
Custom contract
- Everything in Eagle Max
- Custom deployment (cloud / on-premise / hybrid)
- Dedicated customer success team
- Custom SLA & uptime guarantees
- Private threat intelligence briefings
- Executive security reporting
All plans include
Average enterprise breach cost: $4.9M (IBM, 2025). Golden Eagle Enterprise is available for a fraction of one incident.
Questions? +44 7449 766835 · Talk to sales
Customer Success
Trusted by Security
Leaders Worldwide
"Zero successful BEC incidents in the six months since deployment. Our clients now cite our security posture as a primary reason they chose us over larger competitors. That is a direct commercial benefit we did not expect."
"We eliminated our chargeback exposure by 94% in the first quarter. The PCI-DSS compliance audit we had been dreading passed without a single finding. The evidence layer did the documentation work for us."
"Our NDPR audit passed on the first attempt. The auditor specifically commented on the quality of our evidence documentation. What they did not know is that PulseADT was generating those records automatically from the moment compliance monitoring was enabled."
Full-Spectrum Protection
One platform.
Every attack surface.
Cloud Security
Stop cloud breaches before privilege escalation completes.
Lateral movement, credential theft, misconfigured IAM - PulseADT correlates signals across AWS, Azure, and GCP in real time, containing threats before they reach critical assets.
Explore cloud securityIdentity Security
Every identity. Human, service, AI. Monitored continuously.
Compromised credentials are the leading cause of breaches. PulseADT monitors every human, service, and AI identity - detecting misuse in real time, containing it before damage spreads.
Explore identity securitySOC Automation
Your analysts should be hunting, not triaging.
PulseADT handles detection, hypothesis building, and initial containment automatically. What reaches your team is an outcome with full evidence - not a raw alert queue.
Explore SOC automationSee Everything.
Strike First.
Leave Nothing.
Adversaries move in minutes. PulseADT detects, hunts, and neutralises threats at machine speed - before damage is done.